Navigating the Quantum Leap: Securing the Future with Quantum Cryptography
October 30, 2024 | Juan Simón Cardona Fernández Quantum Cryptography has been making waves recently, with […]
GRC and Cybersecurity in Today’s Business Environment
The evolving security landscape necessitates an understanding of new risks, highlighting the critical role of GRC and information security teams in establishing a secure environment.

Azure Open AI Through a Security Lens
October 2, 2024 | Hugo Cosme Opening Insights In the dynamic realm of artificial intelligence, the […]
Zero Trust Networks in a Remote World
What would the “Olympics of Cybersecurity” look like? They just might be the competitions at DEFCON. Samuel Morris writes about some of his favorite events from previous years as well as some of the ones he's looking forward to this year.
The New Frontier: Securing AI with OWASP’s Cybersecurity Insights
What would the “Olympics of Cybersecurity” look like? They just might be the competitions at DEFCON. Samuel Morris writes about some of his favorite events from previous years as well as some of the ones he's looking forward to this year.

Preparing for Supply Chain Attacks and Overreliance on Critical Software
Cybersecurity incidents underscore the importance of preparing for and mitigating the risks associated with overreliance on critical software, whether it’s security software like CrowdStrike, operating systems like Windows, or any other widely used software.

The Olympics of Hacking
What would the “Olympics of Cybersecurity” look like? They just might be the competitions at DEFCON. Samuel Morris writes about some of his favorite events from previous years as well as some of the ones he's looking forward to this year.

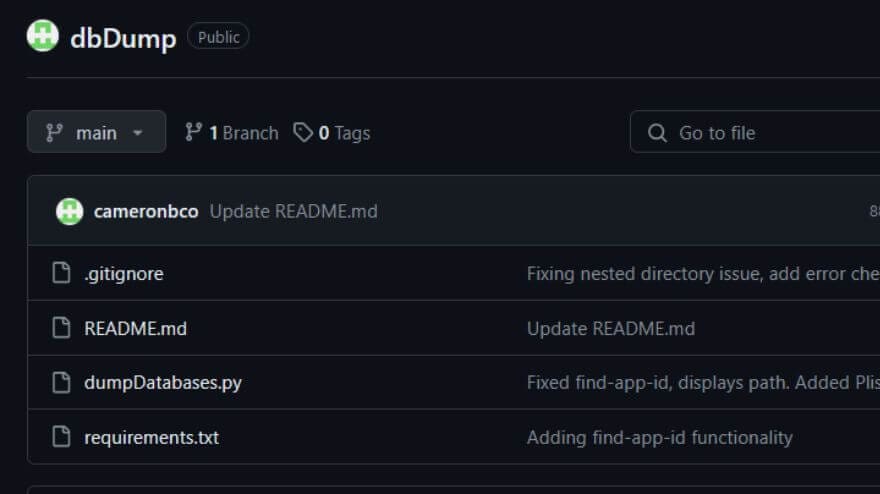
dbDump: An iOS Tool
Need a tool to automate dumping .db and .sqlite files from jailbroken iOS devices? Exfil's got you.
Security Considerations in an Extended Reality (XR) World
Apple Vision Pro is designed to blend digital content and apps into your physical space. Unfortunately, that comes with security risks too.

The Promise of AI in Information Security
Do we blindly depend on AI, expecting it to be a panacea for all security challenges, or do we embrace it with full awareness of its potential and limitations?